
This article has not been completed yet. However, it may already contain helpful Information and therefore it has been published at this stage.
First, the onprem machine needs to be onboarded in Azure Arc.
You can read more about this in one of my earlier blog posts (see link).
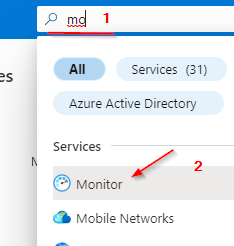
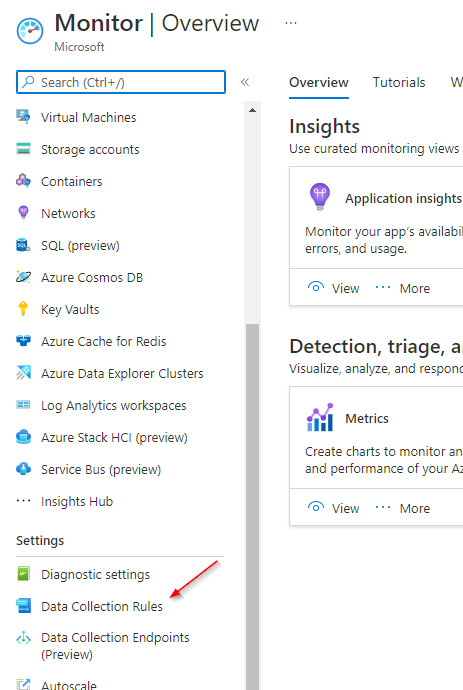
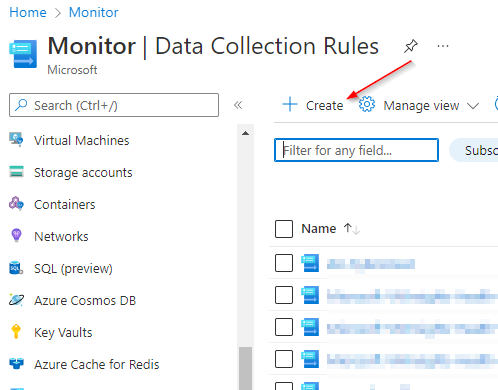
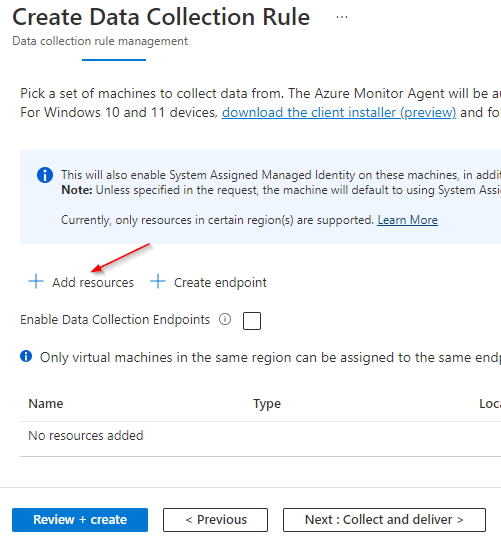
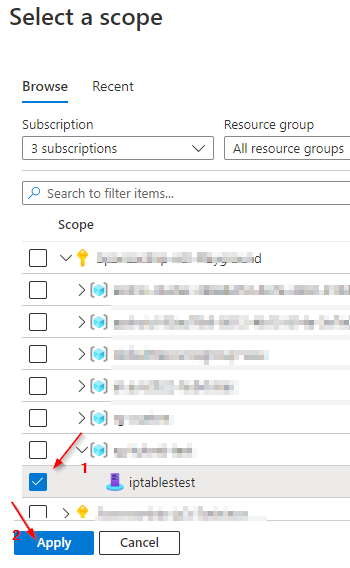
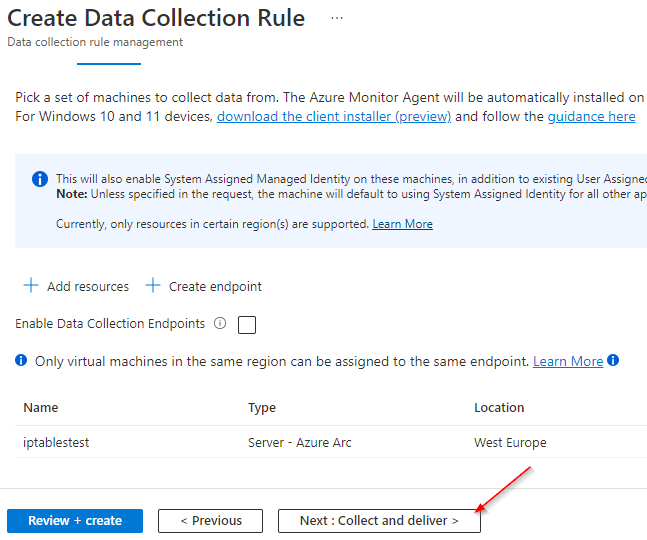
Next, a data collection rule needs to be created.
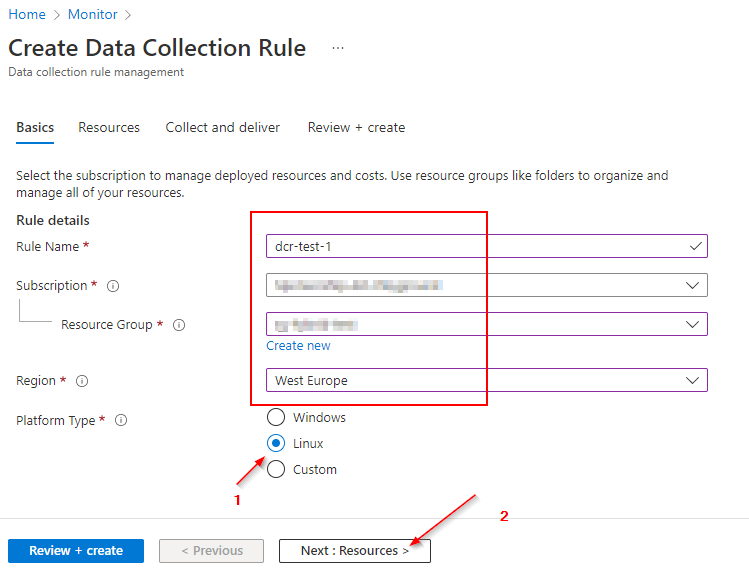
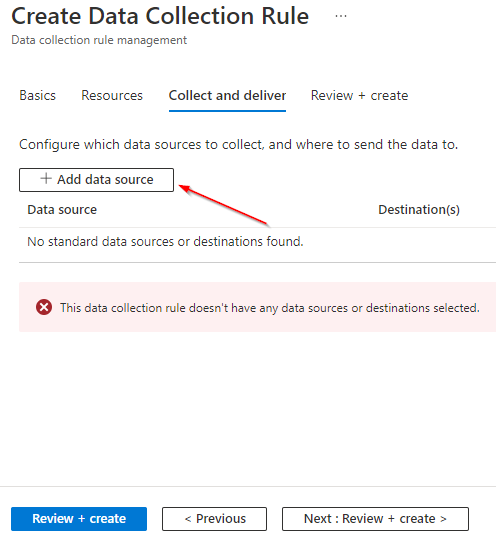
At this stage, we only want messages from the user facility. So we set all other facilities to "none" and "LOG_User" to "LOG_INFO".
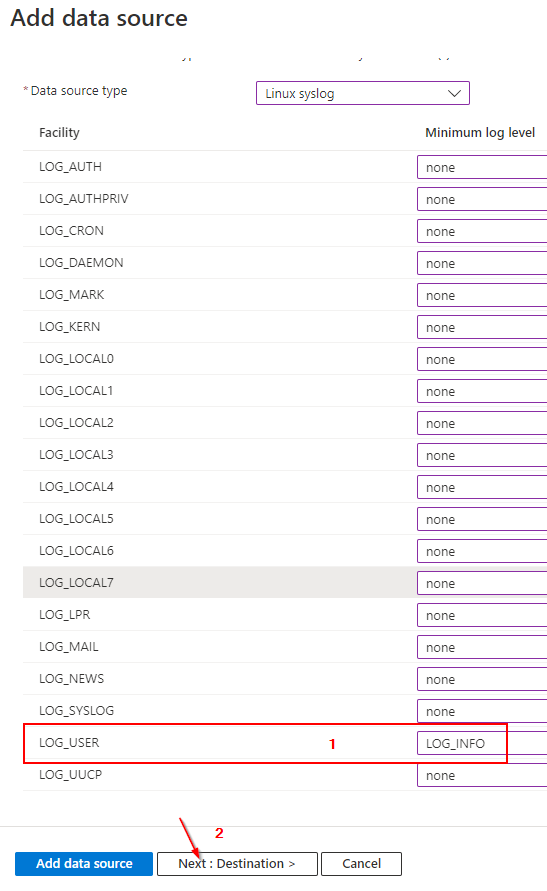
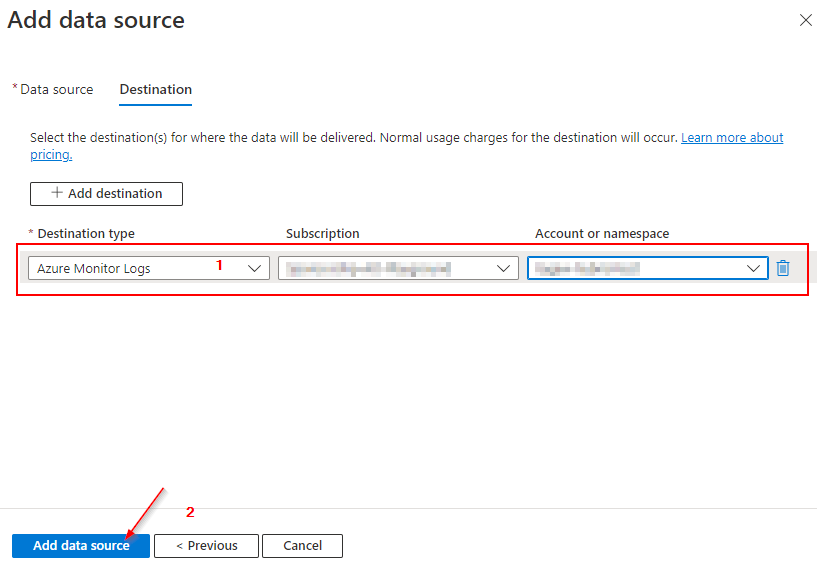
Now you can choose the right logging destination. I assume that there is already a Log Analytic Workspace available.
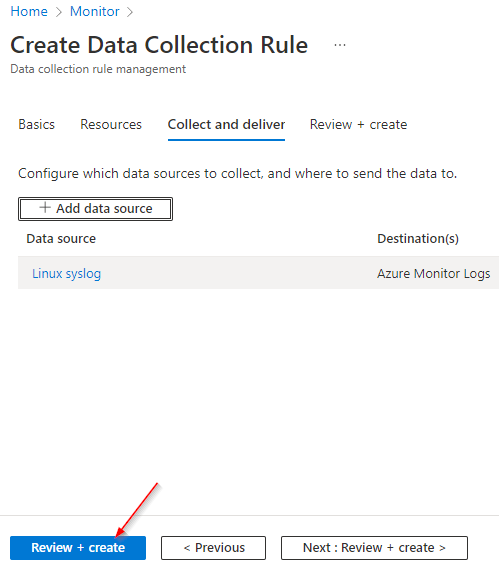
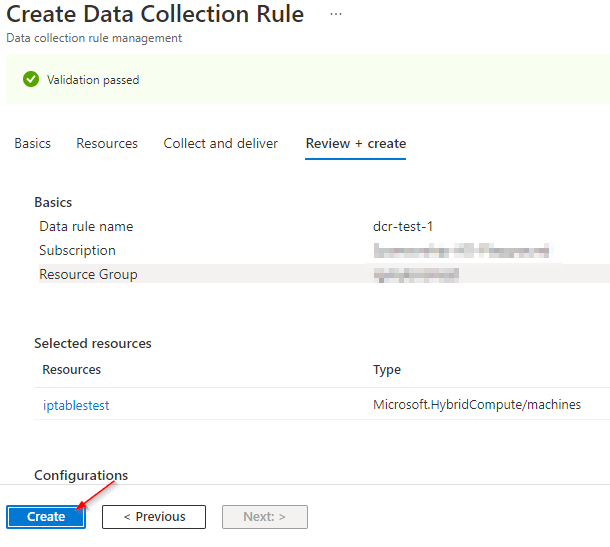
Creating a Data Collection Rule triggers the installation of the AMA Agent via the ARC Agent (Azure Connected Machine Agent).
As a result you will find a new heartbeat table in your Log Log Analytic Workspace.
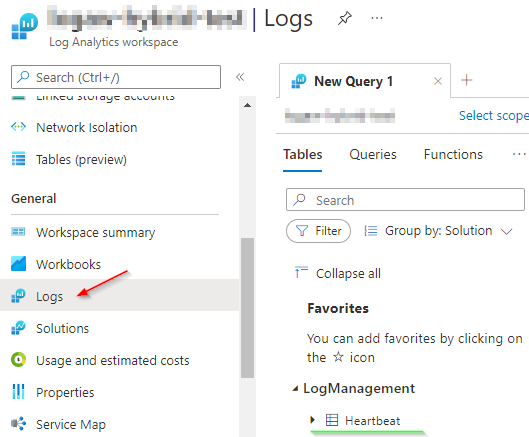
Consequently, there is a connection between the new delivered agent and Azure.
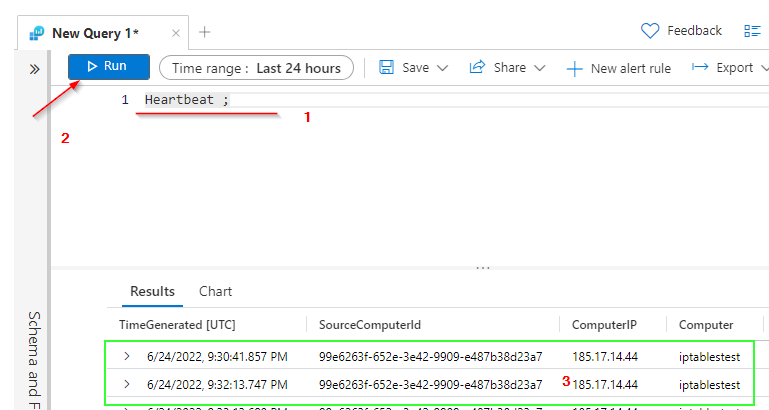
But how do we get syslog info now?
Again, I already created a blogpost where I discuss how to set up an rsyslog server (see link). So I won't go into more detail here.
In a nutshell, I just set up an rsyslogserver that listens via port udp/tcp 514 and only allows connections from 127.0.0.1 (localhost), in other words, from itself.
Now I just sent a test message using the following command.
echo "<14>Test UDP syslog message" >> /dev/udp/127.0.0.1/514
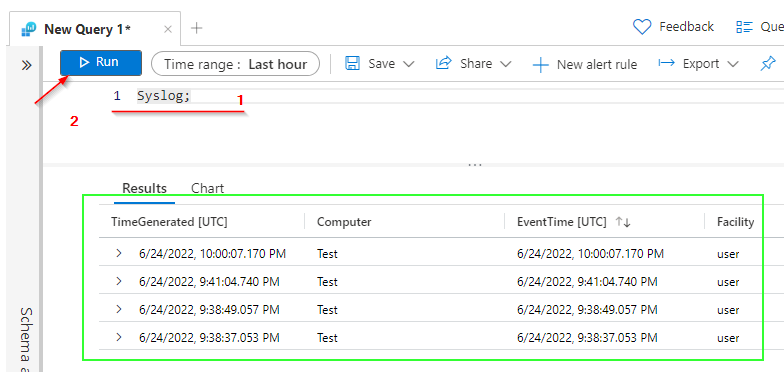
echo "<14>Ubuntu UDP This is just a simple log line to Port 514 via UDP" >> /dev/udp/127.0.0.1/514
echo "<14>Ubuntu TCP This is just a simple log line to Port 514 via TCP" >> /dev/tcp/127.0.0.1/514Lastly, I tried to query the syslog table, which should now be present.
Expected Result:
Alternatively, you can also use the included program "logger".
logger -n 127.0.0.1 -P 514 "This is just a simple log line to Port 514 via UDP"
logger -n 127.0.0.1 -P 514 -T "This is just a simple log line to Port 514 via TCP"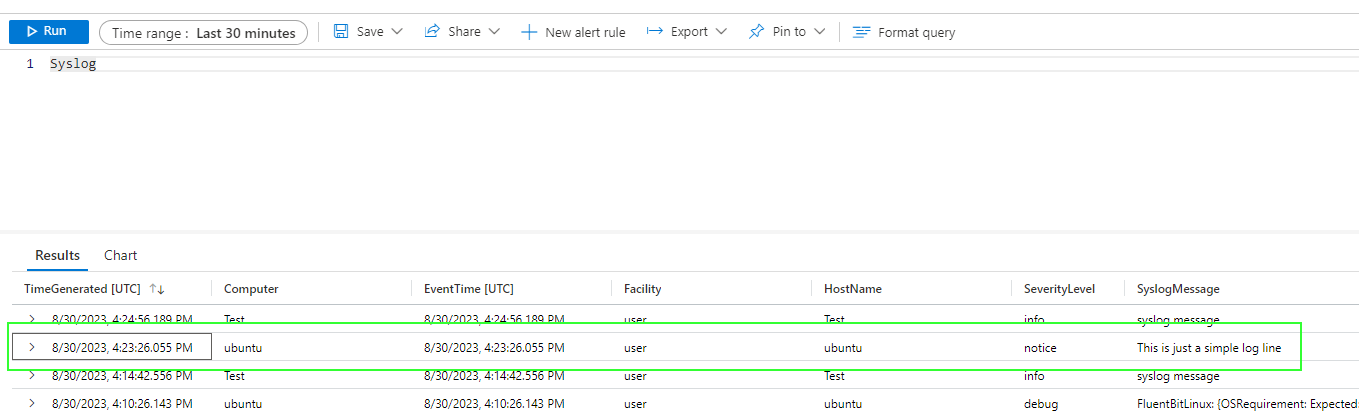
References:

https://it-infrastructure.solutions/onboarding-azure-arc-linux-ubuntu/
https://it-infrastructure.solutions/install-rsyslog-on-ubuntu-20-04/

https://docs.microsoft.com/en-us/cli/azure/monitor/data-collection/rule/syslog?view=azure-cli-latest
Linux logger Command Usage Tutorial with Examples


